I recently watched a captivating, 16-minute video. It documented how a team of hired hackers rather easily broke into the headquarters, substations and other facilities of what appeared to be a secure rural electric cooperative.
The co-op, which was somewhere in the Midwest, hired RedTeam Security of St. Paul, Minn., to test the security of their facilities.
RedTeam provides security services such as penetration and social engineering testing. The company promotes its hackers as “ethical,” meaning they don’t break anything. However, team members will lie to people, crawl over fences at night, pick locks, block security systems, dismantle equipment, and tinker with computer networks to gain access.
The most encouraging moment in the video came when a suspicious co-op supervisor denied building access to hacker team members. The hackers had presented themselves to the receptionist as tech workers who wanted to test the company’s Internet speed. Ironically, while the hackers waited in the reception area to see a supervisor, another co-op employee volunteered unsuccessfully to escort the hackers into the plant.
After their failed attempt at social engineering – or “people hacking” – the team turned to old-fashioned burglary. They checked out the office complex during daylight and broke in at night.
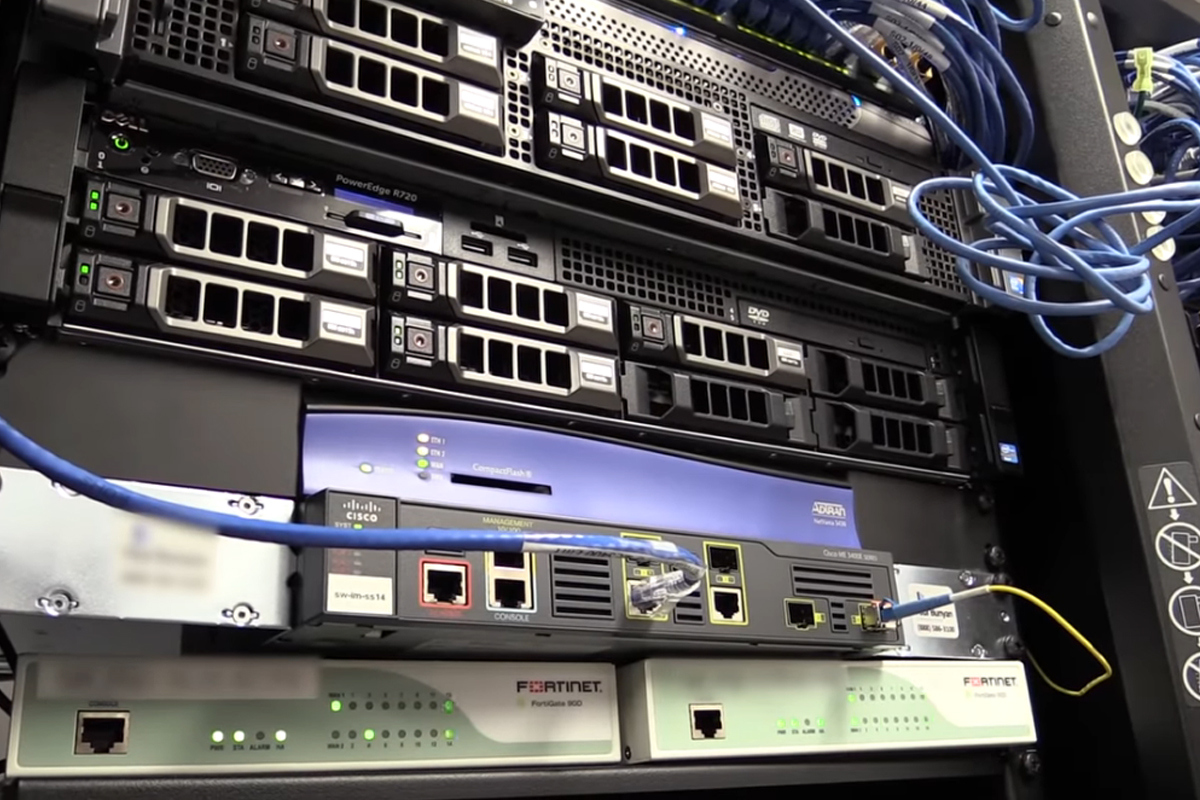
Part of the team entered the grounds through a neighboring woods. The other half just parked in the employee lot. Specialized tools helped them unlock a couple of closed doors and within moments, it seemed, team members were gleaning information from random mobile devices. They had the run of the place, including the server room.
Before leaving, the hackers plugged a little device into the co-op’s network to potentially help them download malware and monitor company operations.
The next night, the hacker team started breaking into electric substations. They used a drone to check out and help neutralize security equipment such as motion sensors and cameras. Employee identification badges they had cloned also helped them get through locked doors.
They successfully broke into eight facilities, in all, and gained full access to the co-op’s power grid. The scenario eerily echoed warnings from renowned journalist Ted Koppel’s book, “Lights Out: A Cyberattack, A Nation Unprepared, Surviving the Aftermath.”
Koppel’s book explores the possibility and potentially devastating consequences that a successful terrorist attack on one of the nation’s three, largely antiquated power grids could have on millions of Americans. (Read more about Koppel’s book.)
Wars fought with armies and weapons are no longer the biggest threat to the nation’s well being. As many experts attest, cyberattacks are the No. 1 security threat facing the United States.
The video documenting RedTeam’s successful penetration of a co-op with 50,000 customers demonstrates the relative ease in which an attack on a larger grid could be carried out.
The company targeted in the documentary has taken steps to improve its security, the video reports.
The nation, as a whole, has to improve its cyber defenses, too. The potential for cyberattacks on critical infrastructure needs to be taken more seriously by government bodies at all levels and especially at the national level. The obligation to better protect critical infrastructure is shared locally by businesses and organizations provide important services.
Maintaining good physical security in buildings is a critically important component of layered, network security. Access to sensitive areas such as server rooms should be limited to people who need access, for example.
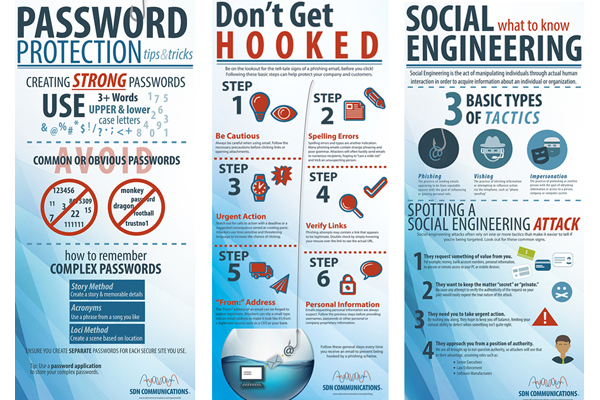
Employee training to guard against social engineering is also a critical component of physical security. In most cases, people are more vulnerable to security lapses than equipment.
Hackers and thieves frequently play on people’s emotions to trick them into giving out information to gain access or valuable information. The deception might come in person or in tainted communications, such as emails or website links. Good, ongoing training for all employees has become a necessity.
Some of the facilities the RedTeam hacked were protected by barbed-wire fences, surveillance equipment and locked doors. In some cases, there were employees on duty. The hackers didn’t have much trouble working around the obstacles, though.
Granted, the hackers were security experts. But thieves can be security experts, too.
Watch the video below. Then take a moment to think about how you would get along for an extended period without electricity or some other important service.
For help in updating your company’s cybersecurity strategy, reach out to SDN.
Request our Trio of Infographics