Like technologies, online threats change. Cyber thieves constantly refine their tactics and tools to create new threats.
A business network that is safe and secure today might be at risk tomorrow. Businesses have to regularly update their security plans and procedures to keep up.
The lag time in maintaining good cybersecurity leaves little windows of opportunity for persistent attackers. Attacks might slip through a gap now and then. Far more often, however, attacks succeed because they get through the weakest link in most companies’ security force: human beings.
Human error is the biggest reason for most cybersecurity breaches. Someone on the inside of a company unwittingly (or maliciously) introduces trouble to an employer’s network by clicking on a bad link or by giving out sensitive information to help hackers gain access.
But even with good employee screening and training, honest mistakes can occur. So what then?
I asked Chad Pew, manager of IT at SDN Communications, about some possible scenarios that business employees might encounter and how they should react.
- What, for example, should an employee do if he or she suspects that they clicked on an infected link or site?
- What if a ransomware message suddenly pops up on their computer monitor?
- What if they think they’ve been the victim of a phishing scam and given out sensitive information? What should they do next?
The moment a cyberattack shows signs of success, minimizing damage to the larger network should become the priority, Pew says. The company can deal later with the responsible employee – ideally in a positive and constructive way.
When ransomware or some other form of malware is suspected of infecting a computer, it’s important to reduce the potential for damage. As quickly as possible, if possible, the employee should cut off the contaminated computer from the rest of the company network, Pew says. Unplug the computer from the Internet or turn it off. If it’s a wireless device, disable it.
After the employee has stopped the potential for problems to spread along other pathways, he or she should report the potential problem to a supervisor or to the IT staff.
Employees should not hesitate to report the problem to others. Accepting blame could be embarrassing or unpleasant. But time is important. The sooner action can be taken to combat a virus or malware, the better, Pew says. A network scan or some other step might have to be taken to determine the next steps.
A phishing scam might require a different response than ransomware or some other type of malware infection. Passwords might have to be changed, for example, or financial agencies used by the organization might have to be alerted to be on the watch for fraudulent transactions.
“It kind of depends on what information they’ve given out. There are just so many varieties of scenarios,” Pew says. “It’s case by case.”
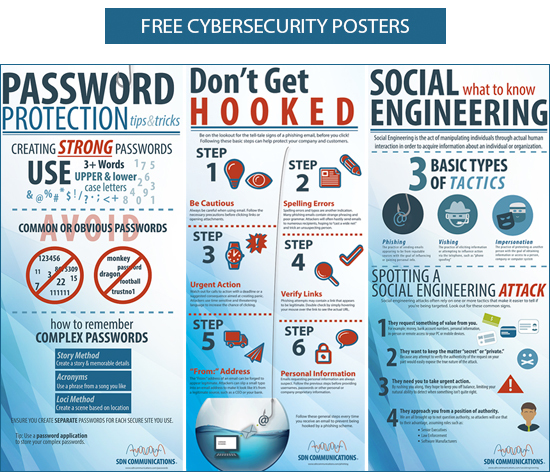
Phishing presents the single greatest threat to information security, according to many experts. Phishing is a form of social engineering in which hackers try to acquire information such as usernames and passwords by masquerading as a trustworthy entity. Phishers might pose as a bank representative or some other service provider that claims to need information for a seemingly legitimate reason.
The best way to combat phishing is to train employees to recognize hackers’ tactics. Hackers commonly use means such as fake emails and other forms of false communication to trick people out of information. Employees must be suspicious and careful any time they’re asked to give out sensitive company information. They should always double-check to make sure that requests are legitimate.
Employees also must exercise caution to avoid exposing a company’s network to ransomware or other forms of malware by letting curiosity get the best of them. They should not click on any links unless they trust the source, Pew says.
SDN Communications is a business broadband provider and cybersecurity leader across South Dakota and Southern Minnesota. Find out more about what they do or reach out by calling 800-247-1442 or through the website.