Bill Burr has been widely described as being the father of the modern-day password. Lately, he’s also become a prominent second-guesser.
The former manager with the National Institute of Standards and Technology, or NIST, has been a subject in national news reports for expressing second thoughts about password-security advice he offered 14 years ago.
In 2003, he suggested that federal employees use passwords that are a series of random characters and symbols, and that passwords be changed frequently. Now, he says, long phrases that people can actually remember might be a better option.
I give Burr, who is now retired, credit for being willing to factor in realities of the times and reconsider his advice. I’m not sure what all contributed to him altering his opinion. However, several factors appear to be at play, especially public frustration with complex passwords that are difficult to remember without being written down. Of course, writing down passwords weakens their security.
Also, it turns out, people tend to react in predictable ways when directed to include a random number or symbol in a password. They might simply change a password from “password” to “Password1,” for example.
“Despite widespread frustration with the use of passwords from both a usability and security standpoint, they remain a very widely used form of authentication,” according to recently updated NIST guidelines. ”Humans, however, have only a limited ability to memorize complex, arbitrary secrets, so they often choose passwords that can be easily guessed.”
The length of a password – also known in NIST-speak as a “memorized secret authenticator” – has been found to be the primary factor characterizing password strength.
“Users should be encouraged to make their passwords as lengthy as they want, within reason,” according to NIST. The same advice applies to passphrases.
Complexity remains important to password security, too, though. Among its other updated guidelines, NIST advises that online services accept the use of spaces in passwords and phrases. The agency also suggests that passwords proposed by users be compared to a master list of unacceptable passwords. The list should include passwords from known breaches, dictionary words and other risky words that might be easily determined.
NIST also points out that in most cases, passwords that are randomly generated are more difficult to guess or attack than user-chosen secrets that must meet length and complexity requirements.
The biggest virtues of passphrases appear to be their extended length and the fact that they might be easier for users to remember. Passwords that are a shorter mix of letters and symbols obviously would be less secure.
I once put the question of passwords vs. passphrases to Chad Pew, who is an expert on password security, and his answer has stuck with me. Pew is the manager of IT at SDN Communications in Sioux Falls. One is not necessarily more secure than the other, he said. “It all goes to their complexity.”
In other words, regardless of whether a person uses a password or passphrase, it needs to be long enough and complex enough to make guessing it or deciphering it with computer equipment difficult.
People with multiple passwords might want to consider using an online management service to store and generate passwords. The up side is that the user only has to memorize one password – the one needed to get into the account. The down side is that in case of a breach, they risk a single point of failure.
We keep hearing that passwords eventually will be obsolete. A user’s fingerprint or something even more secure - such as a person’s heart rhythm – could replace the need for typed or spoken passwords.
In the meantime, computer users probably would be wise to adhere to some old suggestions:
- Keep changing your passwords periodically; don’t reuse old ones.
- Don’t reveal passwords to other people.
- Use two-factor authentication, if available.
The key is to take passwords and passphrases seriously. Don’t settle for something simplistic, such as “password2” or “I like football” as your secret identifier.
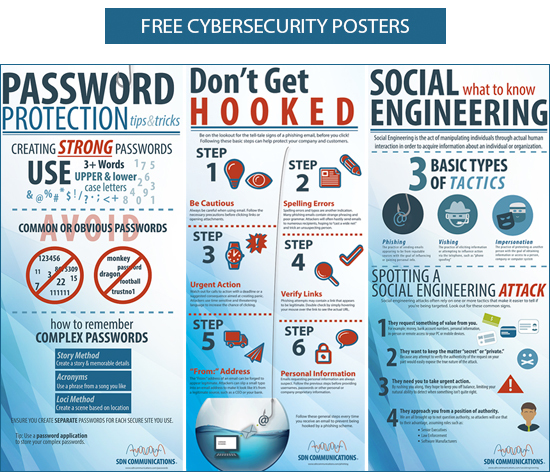
SDN has a series of cybersecurity posters for businesses to help educate employees. Download a copy for your office using the button below.