
Hackers recently demonstrated what they can do to disrupt the flow of gasoline halfway across the continent. The FBI says Russian criminal group “Darkside” is responsible for the ransomware attack on Colonial Pipeline that shut down the system that stretches from Texas to New York.
What would an attack on your industry look like? Healthcare information and technology professionals in the state recently also got an in-depth look at what happened during a ransomware-event-turned-DDoS-attack at Boston Children’s Hospital.
In 2014, the hospital battled with a hacker who wreaked havoc and cost the facility nearly $1 million through lost revenue, reduced employee productivity, the costs incurred to fight the hack, as well as a host of bad publicity.
It’s a really crazy story with so many twists and turns. And the fear of not knowing what was happening next was a very strenuous period for everyone in the hospital. A hospital had never been through anything like this before.
The root cause? A child custody case. A hacker linked to the “hacktivist” group Anonymous blamed the hospital for “torturing” a patient and posted a warning on Twitter.
“As a CIO I’ve been called many things from disgruntled people, but never have I been referred to as an organization that tortures children,” said Dr. Daniel Nigrin.
Nigrin was the senior vice president and chief information officer with Boston Children’s Hospital when the attack happened. Now CIO at Maine Health, he shared the lessons learned with the South Dakota chapter of the Healthcare Information and Management Systems Society, or HIMSS, during its virtual spring forum.
“This had a good outcome in the end, and I feel like we have an obligation to share what we’ve learned,” Nigrin said.

The hacker started slowly with postings on social media platforms and sharing information about people and organizations with ties to the hospital. Nigrin believes that was a way to intimidate those involved in the custody case as it received a lot of local news coverage.
So Nigrin activated the hospital’s Incident Response Team, a broad group of hospital staff that dealt with emergencies such as weather incidents or the Boston bombing, which was nearing its first anniversary. The group met to begin forming contingency plans and asked the question:
What would happen if the hospital had to “go dark” or cut off the internet?
They took action to inform employees about what was going on and reiterated best practices for cybersecurity. But since authorities said nothing illegal had happened, they couldn’t do much more.
Still, the hacker dialed up attacks and changed tactics over the next few weeks – all of which the hospital team could handle.
Then, during the weekend of the Boston bombing anniversary, Easter and Patriot’s Day, the hacker launched a massive DDoS (Distributed Denial of Service) attack against the hospital’s network. In response, the hospital team:
- Took down all externally facing sites.
- Shut down the email system for 24 hours and reinforced employee education on phishing attacks.
- Brought in a third-party vendor to help.
“Talk about disruptive — we were cutting patients off from portals to access their information. We were in the midst of a walkathon pledge drive with donations going through an online site,” Nigrin said.
The authorities were now involved and advised the hospital team against talking with the local news because groups such as Anonymous thrive on media attention. However, The Boston Globe’s next headline read “Cyberattack hits Children’s Hospital” and it all became public knowledge.

“It hit the news because we had alerted all of our staff when we turned the email and web back on,” he said. “When you have 15,000 people aware, it’s understandable how something would leak.”
But everything changed when another Anonymous hacktivist spoke up and tweeted out to its 1.24 million followers:
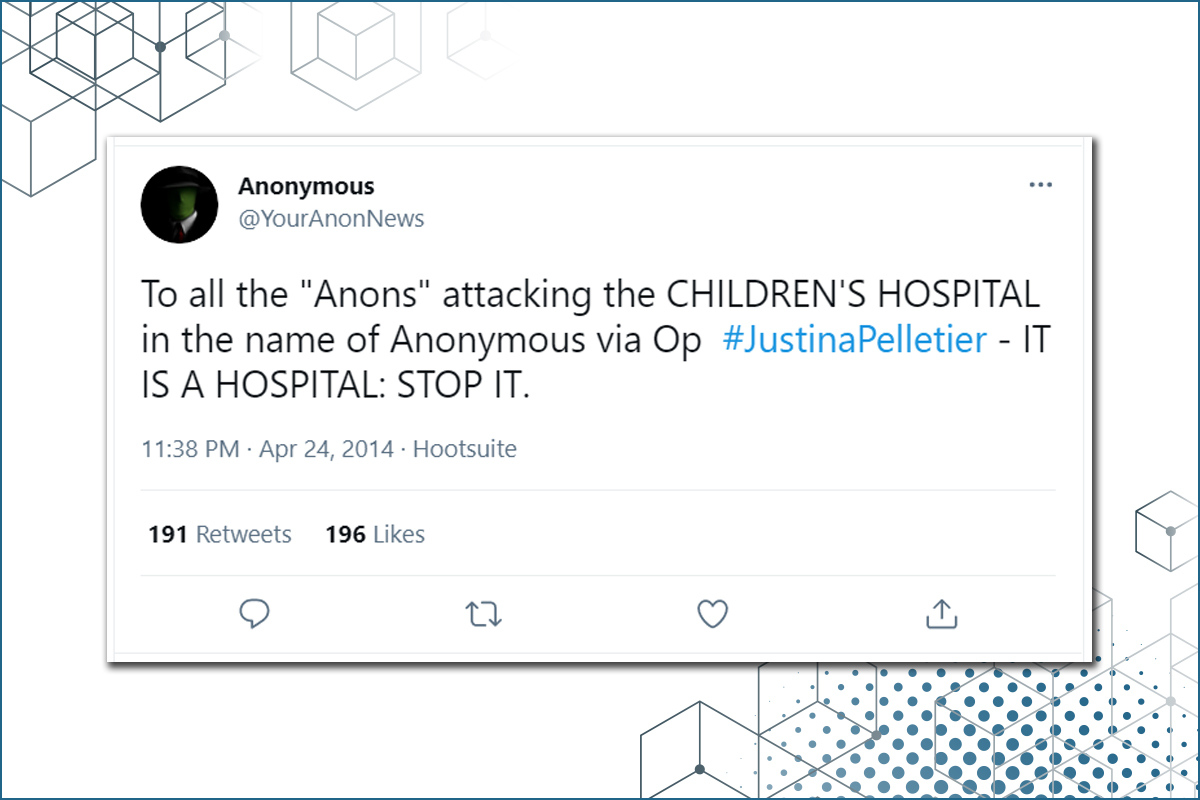
“To all the “Anons” attacking the CHILDREN’s HOSPITAL in the name of Anonymous — IT IS A HOSPITAL: STOP IT.”
Within 12 hours, Nigrin says the attacks slowed to a trickle but there were two big costs to deal with:
- The technology it had to deploy in an emergent way for DDOS protection and penetration testing.
- The revenue lost from philanthropic donations.
The hospital never “went dark” but together, he figures their efforts cost the hospital close to $1 million.
The moral of the story, Nigrin said, is that healthcare organizations must pay closer attention to cyber threats and prioritize efforts against them — far more now than ever before.
While he spoke from the perspective of a healthcare organization, the advice he shared on how to prepare for an attack is relevant to nearly every industry.
DDOS countermeasures are critical.
He says you need to know what systems or features within systems depend on internet access — and have contingency plans for those.
Recognize the importance of email and the need for alternate forms of communication.
Nigrin said their team’s biggest challenge was communicating without email. They took advantage of other modes such as a secure texting platform not dependent on the internet. The bottom line, he said, is ensuring you have multiple communication options, from phone trees to paper lists of cell numbers, and an emergency notification system like those used for weather or active shooter situations.
“We have those platforms deployed now,” he said. “With all of those approaches cobbled together you can reach a good amount of individuals but it’s not done without planning. That was the biggest challenge — not having thought through the communications aspect as much as we needed to.”
Security initiatives are important.
Nigrin said before the attack, he had a hard time getting buy-in on security measures. But the attack was the “aha” moment for many hospital leaders who needed to understand the threats and what was needed to protect against them.
Secure teleconference meetings.
Hackers can access information from insecure teleconferences — so do not put the passcode in the meeting invite.
Separate the signal from the noise.
The adage “if you see something, say something” applies here, Nigrin said. After emphasizing this to hospital staff, employees inundated his team with reports of weird phone and email messages. While most of it was spam, they were now reporting everything, which was good.
Awareness and education are important but not only within organizations. He says it helps that more companies are talking about security breaches and hacking than they were in 2014.
“There are benefits for the collective to not keep things under wraps — the only way to improve is to share our encounters,” he said.
As for what happened to the Boston Children’s Hospital hacker, it took some time, but the FBI got their guy as he fled the country. The hacker and his wife were on a boat off the coast of Cuba that had to put out a distress call to be saved. A cruise ship came to the rescue and the FBI was waiting for them to debark in Miami. Five years after the attacks, a federal judge sentenced Martin Gottesfeld to ten years in prison and nearly $500,000 in court costs.
SDN Communications was a sponsor of the SD HIMSS forum. In addition to high-speed broadband internet, the company offers cybersecurity mitigation services including Managed DDoS Protection and Managed Firewalls for businesses and organizations across South Dakota.



