Managed DDoS Protection with SDN
Why Your Business Needs Managed DDoS Protection Services
DDoS attacks can disrupt critical business services such as the internet, email and websites, causing your customers, vendors and employees frustration, time and potential lost revenue. SDN's Managed DDoS Protection service monitors all incoming internet traffic on your network. Our system mitigates the effects of DDoS traffic delivery to your network.
What is a DDoS attack? How does a DDoS attack work?
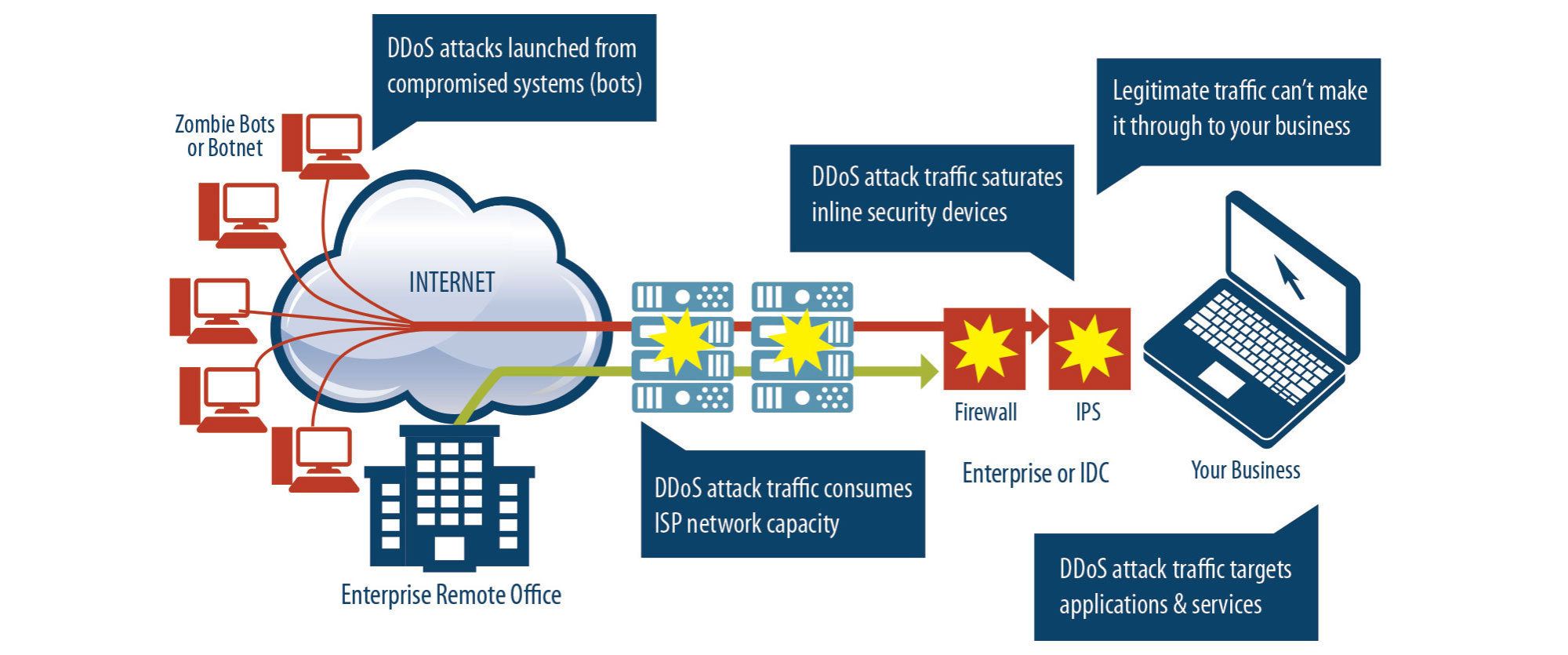
A distributed denial-of-service (DDoS) attack is when a large number of computers or devices flood a website, server or network with traffic all at once. This overwhelming surge makes the system slow down or crash, preventing legitimate users from accessing it. Attackers often use networks of infected devices, called botnets, to generate the massive volume of requests. The goal is usually to disrupt services, cause downtime or pressure an organization for financial or strategic gain.
What does a DDoS attack look like?
DDoS attacks continue to increase in severity. How can you stay protected?
SDN offers multiple levels of protection against a DDoS attack as an additional service to our business internet subscribers. In each package, our Managed DDoS Protection identifies the malicious traffic and has the ability to stop the disruption through mitigation or deploying countermeasures on your internet service. Customers can receive alerts, 24x7 support and scheduled reports, depending on the level of service.
Managed DDoS Protection is a helpful complement to our business internet services, managed firewall services and managed network services. If you depend on the internet to run your business, then you want to make sure your web applications and other services have automatic detection that Managed DDoS Services can provide.
How does SDN’s DDoS protection protect your business?
SDN offers auto mitigation where an attack is stopped automatically with no network technician intervention. The “bad” traffic is rerouted away from the intended destination while legitimate computer requests go through.
The “bad” traffic is rerouted from the intended destination while legitimate computer requests go through. Once the attack stops, all traffic is sent to the customer.
Since legitimate traffic is allowed through while the “bad” traffic is rerouted and discarded, the customer doesn’t know an attack is occurring and can continue with their Internet transactions unaffected.
Managed DDoS Protection Highlights

DDoS Attack Count
Year Over Year
Source: 2021 Year in Review Report

Average Attack Duration
Year Over Year
Source: 2021 Year in Review Report

Average Attack Size
Year Over Year
Source: 2021 Year in Review Report


